The Role of Network Detection and Response in the SOC Visibility Triad
Triangles are the strongest shape. Just examine Grashof’s Criterion for proof. This criterion will tell you that the connection points between the sides of the triangle will not move under an applied force. This simple fact is why triangles are found in so many structures around us.
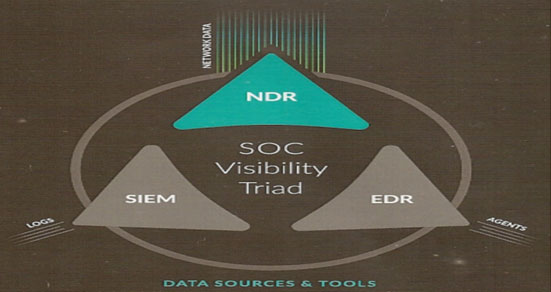
Drawing on this idea, Gartner researchers created a new security model, the SOC Visibility Triad. This model merges endpoint detection and response (EDR), security incident and event management (SIEM), and network detection and response (NDR). All are fundamental tools, but the triad represents a major shift in cybersecurity.
Gartner 2019
Security operations must recognize that threat protection and prevention through ingress/egress (north-south) prevention models are no longer realistic. Knowing that breaches will happen, internal network (east-west) data must be incorporated into threat detection, response and remediation strategies to protect critical assets with a data-driven security strategy.
The everything-but-the-kitchen-sink approach, deploying dozens of point-solution tools, is inefficient and costly. In fact, IDC forecasts a total of $133.8 billion in spending on security solutions in 2022. Ritu Jyoti, VP analyst at IDC, noted that billions of dollars are unwisely spent on products like IDS and similar breach detection tools that will generate many alerts but without the contextual information to do the final identification of the threat. The problem with these “point-in-time-decision” detection tools is that they will only be able to alert on the known malicious traffic, and most new attacks (until becoming familiar to the different security tools) will go undetected. As industry statistics are still averaging around mean time to detect of about 120 days, it is clear that these tools will not provide the needed visibility to mitigate the threats.
The reason that NDR is an essential smart investment is that at the end of the day, everything leaves a network footprint. A next-generation NDR can backtrack and visualize where files were downloaded from, where they were placed afterward, who accessed them and what servers or data were exposed as a result. All these could be answered easily by the right NDR tool that analyzes, classifies and indexes all that information in order to provide clear context to any alert, whether it was generated by an EDR, SIEM correlation or any other security tool.
EDR is useful but not enough
An effective EDR tool focuses on identifying and interpreting anything unusual that’s living on endpoints. However, EDR comes with a catalog of challenges:
- An EDR agent must be installed on each endpoint.
- Security staff must be expertly trained in detection and response.
- Attackers can disable and tamper with EDR agents.
- EDR alerts don’t provide context into broader breach campaigns that might not manifest in the same endpoint.
- Inaccurate security rules/heuristics/algorithms often lead to false-positive alerts.
- Excessive noise and network blind spots lead to missed threats.
In the 2020 Ponemon State of Endpoint Security Risk study, organizations reported that 34% of endpoints connected to the network were unsecured. Clearly, network activity must be monitored and analyzed not just at entry and exit points, but also at internal corridors.
SIEM is useful but not enough
SIEM normally collects, aggregates and correlates a variety of data sources from different IT and security systems: host systems, applications, network and security devices, you name it — SIEM systems can identify and categorize symptoms of an incident and conduct specific analyses, but they have many shortcomings:
- They’re vulnerable to tampering as attackers can turn off, modify or erase logs.
- Storing, extracting and analyzing log data is labor- and resource-intensive.
- Log data by its nature is limited to metadata and doesn’t contain the actual data needed to do the deeper dive.
- Without log enrichment, large amounts of log data slow down searches and create a lack of context.
- A deluge of true and false positives and useless log data leads to fatigued and distracted security.
The evidence is clear: A mature security program must include more than just endpoint visibility (EDR) and SIEM logs. What’s the missing component? NDR. As a matter of fact, NDR might be the missing point that makes those other two security controls even more effective.
NDR and the power of three
NDR adds network visibility by collecting and analyzing wire data from the communications between each subsystem and devices connected in your network environment — that network can be in a datacenter, corporate on-premise or cloud-based. The network protocols create wire data (network packets) that are difficult to tamper with, so wire data is viewed as the most objective source of information when investigating threats — as the saying goes “Packets never lie.”
When combined with EDR and SIEM, NDR completes the Triad and provides visibility into network communications and the specific activities performed within those protocols. Now, anomalous behavior and activity can be detected both at the perimeter and even more importantly by looking at the internal traffic moving latterly, where typically your next-gen firewalls are not deployed. The network insights and artifacts provided by the NDR will then be used to provide deeper context to enhance log data and endpoint alerts.
Automation is a prime way to address talent shortages and more complex threat landscapes. In fact, a 2019 study revealed that 66% of enterprises responded to one to 25 cybersecurity incidents per month, while 26% face 25-99 per month. Automated and augmented investigation and response capabilities become a reality with NDR. It provides immediate visibility and context while reducing complexity and time to respond.
Moreover, NDR captures the pieces of evidence that are most critical to make the final determination of the attack.
Not all NDRs were created equal
Adding NDR to your security program can improve the overall maturity of your program. However, deciding which platform offers the best functionality with the most convenience is a challenge. Enter WireX Systems.
While most NDR vendors are focused on the detection part in order to be the first to provide the alert, WireX Systems NDR is also focusing on the investigation in order to help your team move from alerts and symptoms to diagnostics and remediation.
WireX Systems’ powerful platform address serious issues underlying the traditional network analysis. As mentioned earlier, network security and visibility must extend beyond your network’s perimeter and concentrate on internal security threats (east-west traffic). However, the ability to analyze network data and store it efficiently has two main challenges: storage and complexity to use the mountains of packet data.
Storing packet-level information was always limited to storing only a few days of payload data (and the rest is high-level metadata). We all know the industry statistics of time to detect that range around 120 days, so by the time we would need to use those packets, they would already be long gone.
The second challenge is the complexity to work with the “bits and bytes” and transform them into something insightful. Most packet-based systems are very complicated to operate and will require a network expert as well as a security expert to operate them, so even in the case where you actually have the packets, it would be pretty hard to put them to good use.
If this sounds overwhelming for a human analyst, then you are right. They would need to be familiar with each network protocol and know it inside and out in order to figure out what really happened.
WireX Systems’ main differentiators are exactly around these two challenges — WireX provides at least 180 days of payload information combined with an automatic analysis that does the heavy lifting of the analyst for him.
Comprehensive visibility, network analytics and deep understanding of the complex relationships in your network without sifting through vast amounts of data are what make WireX Systems Contextual CaptureTM technology invaluable. It removes the need for time-consuming and non-replicable processes like raw packet analysis. A fully reconstructed OSI stack and months of in-depth network activity reveal relationships and interactions among network components that would otherwise remain hidden to the analyst. Threat intelligence from Contextual Capture enables you to move from alerts and symptoms to diagnostics and remediation by responding to threats with decisive context and even finding time to do proactive hunting.
Yes, ample context for detection and response is an ingenious benefit of Contextual Capture, but it does not stop there. While the large volumes of data generated by analyzing network traffic are overwhelming traditional network detection tools, WireX Systems’ NDR solves this with Big-Data Analytics, including high-performance databases, ultra-fast response times and scalability to store many months of forensics history and intelligence. You can use your captured activities to visualize, detect, trace and analyze network anomalies so responses are decisive and directed. With ready access to the past and present, it’s easier to identify and understand specific attack techniques.
You can also use these features to their fullest with WireX Systems Incident Management Framework, a powerful central hub that streamlines investigation and response processes and accelerates knowledge sharing across team members.
In recent news
Garmin, an electronics firm known for GPS systems, brought its networks back online July 27 after a ransomware attack, according to an article by AFP. The July 23 attack disrupted Garmin’s company communications and customer-facing services. Garmin has said only that it suffered a cyberattack that encrypted some of its systems. As the number of security incidents continues to rise, security professionals need to adopt technologies that help them accelerate and simplify the response process. Don’t get stuck in the routine of purchasing isolated point-solutions for your security concerns, hoping that something will eventually stick. Ignoring the opportunity to leverage the intelligence and data already at your fingertips by using an NDR tool is like building a bridge with circles instead of triangles.
Contact WireX Systems today to leapfrog from chasing alerts and symptoms to having clear context for diagnostics and remediation.






