Ne2ition NDR
Detection Alone Isn’t Enough
Traditional NDR tools focus on anomaly detection and alerting. But alerts don’t answer the most important question: What actually happened?
Net2ition NDR combines detection with proof, enabling security teams to reconstruct events with certainty.
AI-driven detection. Full visibility across cloud and on-prem
Net2ition NDR’s AI-powered platform continuously captures and retains full network context, transforming traffic into defensible, investigation-ready evidence.

Most detection tools only collect detailed network data after something suspicious is triggered.
Net2ition NDR operates differently. It continuously collects and analyzes full payload activity across the network, enabling organizations to reconstruct real behavior, validate exposure, and prove incident impact with confidence.
Ne2ition NDR retains months of network activity data — sessions, payload context, and behavior. With our AI analytics and automated workflows, analysts can easily reconstruct incidents, validate impact, and provide defensible answers during investigations.
At the core of Ne2ition NDR is AI that transforms network activity into evidence: from sessions and protocols to data movement and user behavior. You don’t just detect anomalies—you understand what actually happened.
Why Ne2ition NDR is different
Most NDR tools provide:
- Alerts
- Metadata
- Limited retention
- Correlated logs
Net2ition NDR provides:
- Full packet behavioral context
- Up to 12 months of retained forensic evidence
- Human-readable reconstruction of activity
- Investigation-ready answers in minutes
It doesn’t just flag anomalies — it reveals the story behind them.
AI That Reveals the Evidence
Ne2ition NDR’s AI continuously analyzes network traffic, sessions, and behaviors — turning raw data into investigation-ready evidence. See exactly what happened, who was involved, and how activity unfolded — in minutes, not hours.
- Automated reconstruction of sessions and data flows
- Context-rich evidence for audits and investigations
- Fast, actionable insights with minimal analyst effort
From alerts to answers, Ne2ition NDR’s AI turns visibility into verifiable proof.

Key Features
Real-Time Threat Detection
Identify behavioral anomalies as they happen, across users, apps, and assets
Extended Payload Retention
Store and analyze months of full payload data using WireX System’s ultra-efficient compression engine
Automated Investigations
Built-in IR engine reconstructs incidents and maps out the full impact — even from third-party alerts
Insider Risk Management
Detect suspicious or policy-violating behavior with behavior-aware baselining
Cross-Environment Visibility
Cloud, on-prem, or hybrid — see everything in one place
Compliance at Scale
Support audits and policies with complete, long-term forensic evidence
What’s Under the Hood?

Packet Collection
Deployable on-prem or in the cloud, Ne2ition’s software-based collectors analyze traffic at line-rate speeds.

Contextual Capture™
Reconstructs full sessions, files, and user actions for thousands of network activities — continuously.

Big Data Repository
High-speed querying of months of forensic data — with no SaaS storage, keeping your data secure and local.

Investigation, Detection & Response Framework
End-to-end workflow engine for detection, analysis, and collaboration — turning alerts into answers, fast.
Ne2ition NDR - Built on Contextual Capture
Net2ition NDR runs on WireX’s Contextual Capture foundation — a thick data layer that:
- Translates raw packet data into semantic behavioral evidence
- Correlates identity, device, and application context
- Preserves evidence continuously, not just during incidents
This architecture enables:
- Faster root cause analysis
- Confident impact assessment
- Reduced false positives
→ Learn how WireX EvidenceOps integrates network and cloud proof
Operational Outcomes for Better ROI
- Reduce investigation time from days to minutes
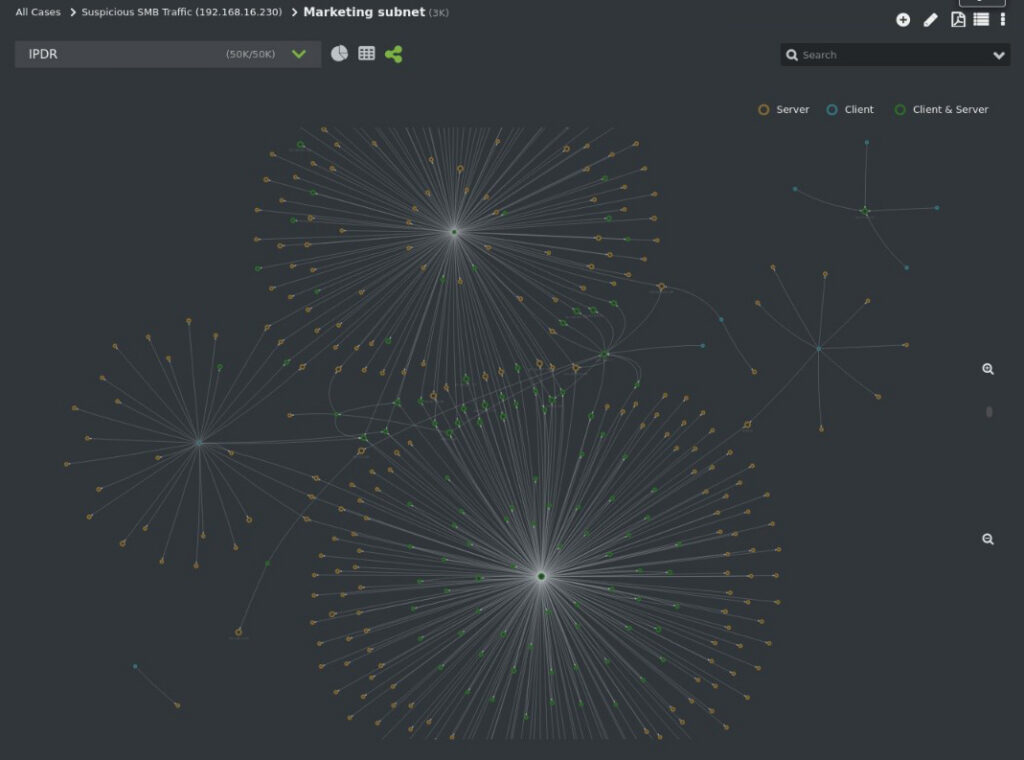
- Trace lateral movement across east-west traffic with precision
- Eliminate log stitching across tools
- Prove real data exposure based on full payload evidence
- Continuously retain complete network activity to detect insider threats and enable proactive threat hunting
- Improve analyst efficiency at every tier


