January 5 2023 |
Amidst a growing cyber threat landscape characterized by multiple attack vectors like remote work, the next zero-day, cloud visibility, application vulnerabilities, end-of-life software (that translate to no security), and increasingly sophisticated attacks like the SUNBURST attacks, business leaders and cybersecurity experts are finding a bastion of security in a new approach known as Network Detection and Response (NDR).
The proliferation of cloud applications, the shift to remote work, and the advent of IoT devices are all events that have conspired to remove the traditional security perimeters usually deployed by organizations to fence their operations from intruders. This is blissful news for the $1.5 trillion/annum cybercrime industry as it exposes all kinds of new attack vectors and strategies for them to explore. However, taking into consideration current investments cybersecurity solutions like EDR and SIEM, NDR provides a comprehensive threat detection system that uses machine learning capabilities to identify anomalous traffic in your systems and provides context to effectively respond to alerts that are generated by these other tools.
In this article, we’ll talk about:
- What NDR is and how it works
- Its importance for your business and,
- how to integrate it with your other security tools
What is NDR (Network Detection And Response)?
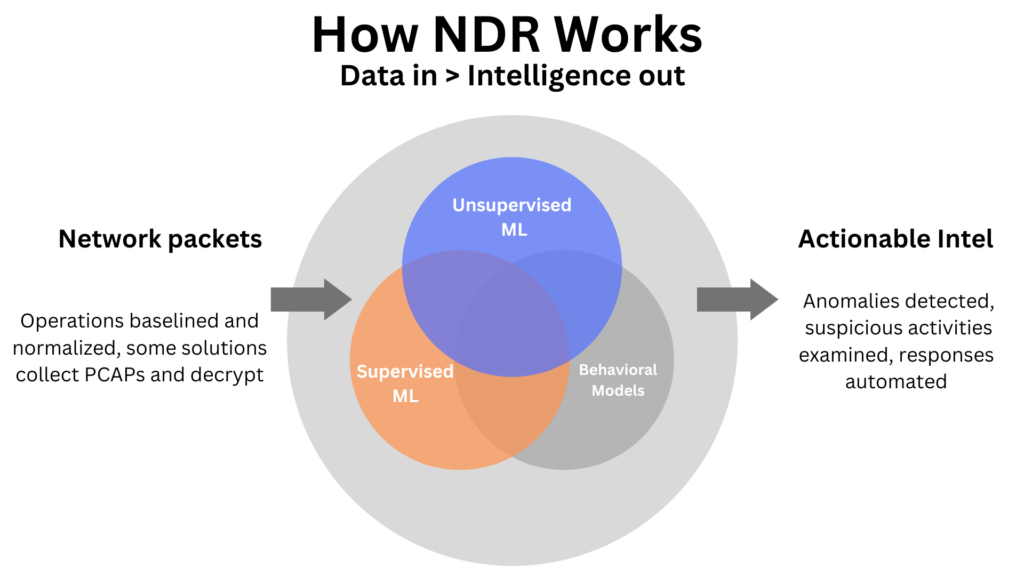
NDR is a security solution that provides a comprehensive analysis of your network traffic, using machine learning methods and deep learning from past attack data to detect threats and respond to them in real-time.
NDR uses behavioral analytics and artificial intelligence capabilities to scour traffic across your network, looking for anomalous activity as defined against previously computed normal conditions of the system. It eschews signature-based detection and instead imposes behavioral rules on the system. Anything operating outside the computed rules of normalcy in your system (which might sometimes be a normal program behaving in an unusual way) or following the trend of a known attack pattern, is flagged, reported as a potential threat, and dealt with by the NDR solution.
EDR vs. NDR
EDR solutions focus on detecting threats at endpoints like computers or servers. They are a mandatory tool in every security program but there are also some limitations to relying solely on EDR. These are some of them:
- Attackers routinely try to hide their tools from EDR products.
- EDR has limited visibility into threats inside the network
- EDR store metadata until they detect suspicious activity like a new zero-day attack – while NDR can play back all the activities that were performed in the past (even ones that at the time were considered by the EDR as normal)
Sometimes it is impossible to install an agent (legacy medical environments or utilities infrastructure) and the only way to have visibility is via the network.
NDR, however, shines the spotlight across your entire network, identifying threats not by their effect but by their behavior in transit across the network.
Is A Firewall An NDR?
No. A firewall, often described as a security gate, is a defensive wall deployed at the perimeter of your network to stop intruders in the form of malicious traffic from getting in. It should also be noted that a firewall is not a security device, but merely reduces the exposed attack surface.
An NDR, on the other hand, operates within your system itself looking for intruders that have managed to get past the gate. Once the intruders are detected, the NDR solution halts their attack, investigates the scope and damage, and accelerates immediate mitigation.
NDR is the Evolution of NTA (Network Traffic Analysis)
Network Traffic Analysis (NTA) is a security solution that scans your network traffic, looks for threats, and creates security reports for your team to work on. NTA works by monitoring network availability. When network blockages are detected, the solution goes in to detect the issue and using historical data, identify the potential threat.
As an offspring of this security solution, NDRs take their threat detection capabilities to the next level by using behavioral analytics and machine learning to analyze network traffic and identify threats. NDRs also incorporate a “Response” capability that enables them to take action against identified threats. NDR is the evolution of NTA from a simple monitoring tool to a comprehensive defense system that can both detect threats and take action against them.
How Does NDR Work?
To perform its ultimate function of identifying threats that are trying to slip into your network through traffic and terminating them, an NDR solution has a few key methods:
Investigation
One of the core functions of an NDR solution is to investigate all instances of anomalous traffic within your network. As we said earlier, this can sometimes be a normal program executing in an unusual way. The solution shines a perpetual light on your network traffic and all unusual traffic is analyzed for suspicious activity. The result of this analysis is used by the NDR solution to generate an automated response.
Intelligence Management
NDR solutions take on a central role in managing your threat intelligence by consuming data from both internal and external sources to learn more about current threat patterns. This data is used to inform the threat detection processes to make the identification of new threats easier. This data can also be shared with other integrated tools as part of a central threat management architecture.
Threat Prevention
With the data generated from the investigation of anomalous activity in your network, compared against threat intelligence from internal and external sources to identify known threat patterns and possible attacks, NDR solutions then generate an automated response to suspicious activity to head off cyber attacks.
This often includes working with other security tools to block an attack vector or neutralizing an intruder with a firewall. They also create alerts and incident reports to inform your security teams of potential threats.
Cyber Incident Detection
Using behavioral analytics capabilities, NDR solutions monitor your network for all forms of unusual activity. The NDR uses rules-based detection methods to detect incidents that are out of the ordinary. These are then investigated for suspicious activity.
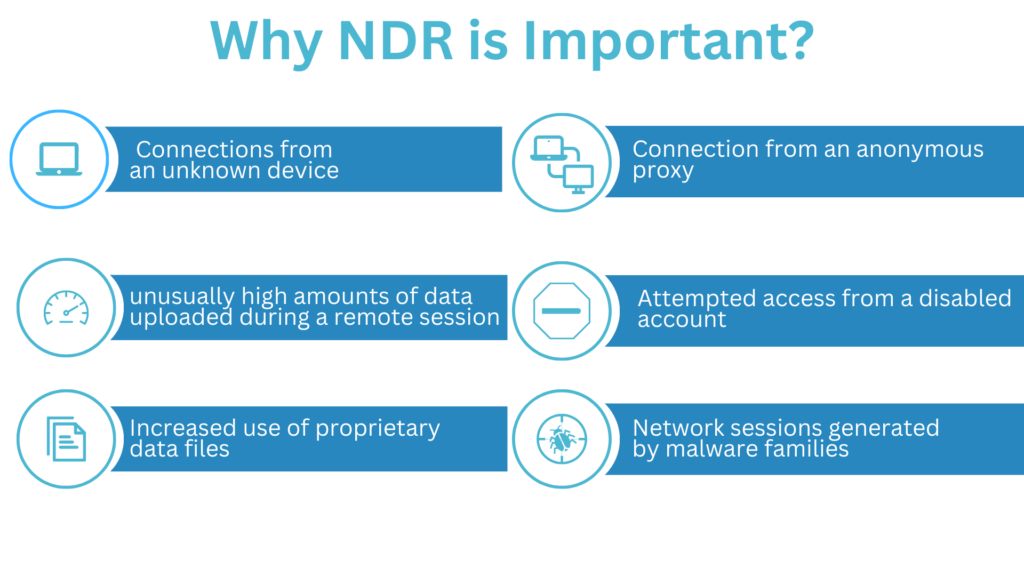
Why Is NDR Important For Your Company?
NDR as a comprehensive security solution (especially if deployed alongside other tools) is an immensely valuable tool in your security arsenal. From its threat detection capabilities to AI and machine learning methods that enable it to identify and respond to threats in real-time and automation of security tasks like creating alerts, it makes securing your systems a lot easier. Let’s take a closer look at some of the benefits of NDR.
Benefits Of NDR
AI and Behavioural Analytics: NDR uses behavioral analytics to create a rules-based detection system that identifies anomalous traffic in real-time. The AI models previously known attack patterns and uses this to detect recurring active threats.
Automatic Response and Shut Down of Threats in Real-Time: The NDR generates an automated response to identified threats and works with other integrated tools to stop the attack from succeeding.
SOC Operational Efficiency Improvement: NDR solutions work alongside your threat intelligence management, making it easier to share intelligence between integrated tools. They also create automated alerts and incident reports that your teams can read and act on quickly.
Continuous Visibility: You gain deeper visibility into your network through the constant monitoring capabilities of the NDR. It provides a central location for you to monitor traffic across your entire system, no matter how distributed it is.
Prompt Investigation: Rather than just noting incidents and creating reports, the NDR solution goes one step further to automatically investigate incidents as soon as they are detected. This reduces the response time significantly and gives attackers little time to cause damage to your systems before they are kicked out.
How To Integrate NDR
NDR is a great cybersecurity solution on its own but it works even better when it is integrated with other tools. An NDR provides perspective into the operations of your network, a perspective which other solutions like EDR and SIEM can benefit from. By combining the threat identification data from the NDR with the response capabilities of EDR, for example, you can close up possible endpoints through which an intruder can access your data, thereby heading off a potential attack.
NDR Integration With SOAR
SOAR tools provide a SOC with security orchestration capabilities that allow SOCs to manage all the components of their security stack from a central location and provide automated responses to threats. NDR integration with SOAR provides a direct pipeline of threat intelligence to your SOAR tools with its threat detection and machine learning methods.
Since SOAR tools activate responses through collaboration with other tools, NDR solutions can also serve as the response arm of your security orchestration tools
NDR Integration With SIEM
NDR integration with SIEM provides the latter with network activity data to fill in the gaps in the logging data it typically collects. As SIEM collects metadata from a variety of tools they may have a starting point for an investigation but is lacking the depth of actual activities that were performed on the network (what files were downloaded, by whom, what else did those users do on the network..) This gives you greater threat coverage and provides deeper visibility into your network.
NDR Integration With Public Or Private Clouds
The cloud is an integral part of many enterprise networks today and it is essential to keep an eye on the traffic passing through it. Integrating NDR solutions across cloud environments helps you monitor all traffic in this channel, providing you with even more visibility across the network.
Do I Need NDR?
In a constantly escalating cybersecurity environment where malicious elements are finding new methods to gain access to your systems every day, perhaps the better question is, can you afford not to have it?
An NDR performs a vital function in monitoring network traffic in real time, an important means of access to your systems that previous solutions do not do much about. More than that, the automated response capabilities give you a first responder that could make all the difference between a successful attack and a failed one. And the ease of integration makes it quite easy to slot into your existing security stack.
Achieving Greater Threat Coverage And Response With NDR
Cybersecurity is getting tougher and companies are scrambling to equip everything they can to stay protected. This has become especially relevant as tech possibilities are widening in the coming years. For example, Cloud Computing, 5G, Metaverse, and Electric Vehicles are considered to be top tech areas for 2023. And with this, means heightened attention to potential blind spots.
However, NDR is a vital part of this equipment as it provides coverage and protection for all network traffic coming in and going out of your system. Furthermore, NDR fills in for all the blind spots present in previous security solutions and provides extremely useful threat intelligence to help you stay on top of attacks.
Getting Started With WireX Systems
At WireX Systems we understand your pain when it comes to properly investigating every alert. And currently, the investigation tools that are presently available have failed to meet enterprise business needs. However, with our approach, we deliver comprehensive security intelligence in actual human-readable format, so you can save effort and time when validating alerts and responding to security incidents.
You can learn more on how our technology reduces breach dwell time, but we also have a Whitepaper on the top 3 requirements to turbocharge your incident response.
And, as always, reach out to us and we’ll discuss how to best support your network security needs!






